Design Patterns Training Classes in Springfield, Ohio
Learn Design Patterns in Springfield, Ohio and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Design Patterns related training offerings in Springfield, Ohio: Design Patterns Training
Design Patterns Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX AUTOMATION WITH ANSIBLE
15 September, 2025 - 18 September, 2025 - Fast Track to Java 17 and OO Development
18 August, 2025 - 22 August, 2025 - VMware vSphere 8.0 Skill Up
18 August, 2025 - 22 August, 2025 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
18 August, 2025 - 21 August, 2025 - Object-Oriented Programming in C# Rev. 6.1
23 June, 2025 - 27 June, 2025 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
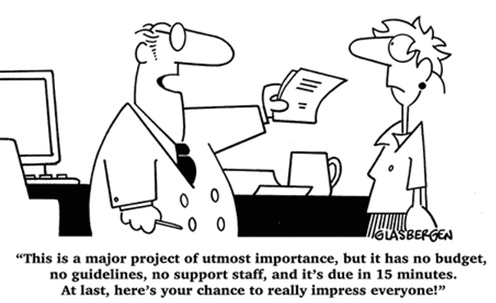 A project manager acts as the primary link between business and technical teams. A project manager is responsible for maintaining the project schedule, developing project estimates, working with external teams and tracking project issues. The project manager belongs to either the technical team or the project management office (PMO). The project manager works with business teams, technical teams, business counterparts, testing resources, vendors and infrastructure teams.
A project manager acts as the primary link between business and technical teams. A project manager is responsible for maintaining the project schedule, developing project estimates, working with external teams and tracking project issues. The project manager belongs to either the technical team or the project management office (PMO). The project manager works with business teams, technical teams, business counterparts, testing resources, vendors and infrastructure teams.
A project manager is often challenged with diagonally opposite views from the business side and technical side. A project manager’s success depends on balancing the needs and emotions of both sides.
Understanding the Requirements
A project manager must familiarize with the project’s requirements as defined by the business or product managers. This will help you understand the business vision behind the project. You will need this knowledge while negotiating with the technical teams.
Understanding the Technical Landscape
A project manager must also understand the technical systems, resource skills and infrastructure capabilities available for the project. Business teams come up with expectations that are sometimes beyond the capabilities of the technology team. It is the responsibility of the project manager to understand the technical capabilities available to the project.
Walkthrough of Business Requirements
This is a critical step in the project delivery process. The project manager must invite members from the business team, technical team, testing team, infrastructure team and vendors. The project manager must encourage the various stakeholders to ask questions about the requirements. Any prototypes available must be demonstrated in this meeting. The project manager must find answers to all questions resulting from the requirements walkthrough. The project manager must get the final version of the requirements approved by all stakeholders.
Managing Conflicts in Timelines and Budgets
All project managers will face the conflicts arising from shortened timelines and limited budgets. Business teams typically demand many features that are nearly impossible to deliver within short timeframes. The project manager must work with business and technical teams to prioritize the requirements. If the project is executed in a product development organization, then the project manager could utilize agile methodologies to deliver projects incrementally. In this case, the project manager may be required to act as a scrum master to facilitate scrum meetings between various stakeholders.
The Art of Saying “No”
As a project manager, you may be forced to say “no” to demands from both business and technology teams. However, it is important to create a win-win situation for all parties when you are faced with conflicting demands. You can work with the stakeholders individually before bringing all parties together. Most stakeholders prefer to work together. The success of a project manager depends on how effectively he or she can bring out the best in everyone, driving everyone towards a common goal.
Finally, the job of a project manager is not to satisfy the demands from all corners. The project manager must identify the essential deliverables that will meet the business needs, with a solid understanding of what is possible within the limits of technology.
Related:
A business rule is the basic unit of rule processing in a Business Rule Management System (BRMS) and, as such, requires a fundamental understanding. Rules consist of a set of actions and a set of conditions whereby actions are the consequences of each condition statement being satisfied or true. With rare exception, conditions test the property values of objects taken from an object model which itself is gleaned from a Data Dictionary and UML diagrams. See my article on Data Dictionaries for a better understanding on this subject matter.
A simple rule takes the form:
if condition(s)
then actions.
An alternative form includes an else statement where alternate actions are executed in the event that the conditions in the if statement are not satisfied:
if condition(s)
then actions
else alternate_actions
It is not considered a best prectice to write rules via nested if-then-else statements as they tend to be difficult to understand, hard to maintain and even harder to extend as the depth of these statements increases; in other words, adding if statements within a then clause makes it especially hard to determine which if statement was executed when looking at a bucket of rules. Moreoever, how can we determine whether the if or the else statement was satisfied without having to read the rule itself. Rules such as these are often organized into simple rule statements and provided with a name so that when reviewing rule execution logs one can determine which rule fired and not worry about whether the if or else statement was satisfied. Another limitation of this type of rule processing is that it does not take full advantage of rule inferencing and may have a negative performance impact on the Rete engine execution. Take a class with HSG and find out why.
Rule Conditions
JAVA SCRIPT TUTORIAL – THE ESSENTIAL ELEMENTS
If you are looking to increase your proficiency in programming, it can make a lot of sense to invest some time into learning how to use JavaScript, or taking a Java Script tutorial. It is one of the most popular and powerful options available today for people to use in programming different parts of their websites. It often finds use in headers, or in interactive features displayed on pages. It allows you to execute many different functions, such as calculation, pulling data from forms, special graphical effects, customized selections, custom security protocol and password systems, and much more. Here are some essential points to keep in mind:
· Java vs. JavaScript – These two languages are not the same. Java uses completely separate files for their headers and classes, and they need compilation prior to execution. Java is used in the creation of applets for pages. JavaScript is much easier and simpler to learn than regular Java, and Java Script tutorials are often significantly more accessible for the average user.
· OOP – OOP, or object oriented programming, is a specific programming technique that simplifies complicated computer programming conceptual issues. Essentially, it lets a programmer treat whole chunks of data (defined either by users, or by the system itself), and modify or access them in specific ways. It does this by classifying different parts of the programming into Objects, Methods, and Properties, which will be discussed more in depth in the future, in other Java Script Tutorials.

When eCommerce companies want to optimize information security, password management tools enable users to create strong passwords for every login.
Better than a Master Pass
A two-factor authentication, a security process in which the user provides two means of identification, one of which is typically a physical token, such as a card, and the other of which is typically something memorized, such as a security code can drastically reduce online fraud such as identity theft . A common example of two-factor authenticationis a bank card: the card itself is the physical item and the personal identification number (PIN) is the data that goes with it.
LastPass 3.0 Premium and RoboForm, security downloads offer fingerprint-based authentication features that can be configured to any computer PC or mobile application. Both are supported by the Google Authenticator mobile app for smart phone and device integration.
LastPass 3.0 is most powerful on-demand password manager on the market. LastPass 3.0 Premium includes mobile support and more features. Dashlane 2.0 is is not as robust, but includes a user-friendly interface. F-Secure Key is a free, one-device version of these top competitors. F-Secure Key is for exclusive use on an installed device, so password safe retention is dependent on proprietary use of the device itself. The application can be upgraded for a small annual fee.
Password Manager App Cross-Portability
F-Secure Key syncs with Mac, PC Android, and iOS devices simultaneously. A transient code is generated on mobile devices, in addition to the two-factor authentication default of the F-Secure Key master password security product.
Password capture and replay in case of lost credentials is made possible with a password manager. Integration of a password manager app with a browser allows a user to capture login credentials, and replay on revisit to a site. Dashlane, LastPass, Norton Identity Safe, Password Genie 4.0 offer continuous detection and management of password change events, automatically capturing credentials each time a new Web-based, service registration sign up is completed.
Other applications like F-Secure Key, KeePass, and My1login replay passwords via a bookmarklet, supported by any Java-equipped browser. KeePass ups the ante for would be keyloggers, with a unique replay technology.
Personal Data and Auto-Fill Forms
Most password managers fill username and password credentials into login forms automatically. Password managers also retain personal data for form fill interfaces with applications, and other HTML forms online. The RoboForm app is one of the most popular for its flexibility in multi-form password and personal data management, but the others also capture and reuse at least a portion of what has been entered in a form manually.
The 1Password app for Windows stores the most types of personal data for use to fill out forms. Dashlane, LastPass, and Password Genie store the various types of ID data used for form fill-in, like passport and driver's license numbers and other key details to HTML acknowledgement of discretionary password and personal information.
The Cost of Protection
LastPass Premium and Password Box are the lowest monthly password manager plans on the market, going for $1 a month. Annual plans offered by other password manager sources vary according to internal plan: Dashlane $20, F-Secure Key $16, and Password Genie, $15.
All password manager companies and their products may not be alike in the end.
Security checks on security products like password managers have become more sophisticated in response to product cross-portability and open source app interface volatility. Norton, RoboForm, KeePass, generate strong, random passwords on-demand. Some security procedures now require three-factor authentication, which involves possession of a physical token and a password, used in conjunction with biometricdata, such as finger-scanningor a voiceprint.
What are the best languages for getting into functional programming?
Tech Life in Ohio
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Nationwide Insurance Company | Columbus | Financial Services | Insurance and Risk Management |
| Owens Corning | Toledo | Manufacturing | Concrete, Glass, and Building Materials |
| FirstEnergy Corp | Akron | Energy and Utilities | Gas and Electric Utilities |
| The Lubrizol Corporation | Wickliffe | Manufacturing | Chemicals and Petrochemicals |
| Sherwin-Williams | Cleveland | Retail | Hardware and Building Material Dealers |
| Key Bank | Cleveland | Financial Services | Banks |
| TravelCenters of America, Inc. | Westlake | Retail | Gasoline Stations |
| Dana Holding Company | Maumee | Manufacturing | Automobiles, Boats and Motor Vehicles |
| O-I (Owens Illinois), Inc. | Perrysburg | Manufacturing | Concrete, Glass, and Building Materials |
| Big Lots Stores, Inc. | Columbus | Retail | Department Stores |
| Limited Brands, Inc. | Columbus | Retail | Clothing and Shoes Stores |
| Cardinal Health | Dublin | Healthcare, Pharmaceuticals and Biotech | Healthcare, Pharmaceuticals, and Biotech Other |
| Progressive Corporation | Cleveland | Financial Services | Insurance and Risk Management |
| Parker Hannifin Corporation | Cleveland | Manufacturing | Manufacturing Other |
| American Financial Group, Inc. | Cincinnati | Financial Services | Insurance and Risk Management |
| American Electric Power Company, Inc | Columbus | Energy and Utilities | Gas and Electric Utilities |
| Fifth Third Bancorp | Cincinnati | Financial Services | Banks |
| Macy's, Inc. | Cincinnati | Retail | Department Stores |
| Goodyear Tire and Rubber Co. | Akron | Manufacturing | Plastics and Rubber Manufacturing |
| The Kroger Co. | Cincinnati | Retail | Grocery and Specialty Food Stores |
| Omnicare, Inc. | Cincinnati | Healthcare, Pharmaceuticals and Biotech | Pharmaceuticals |
| The Procter and Gamble Company | Cincinnati | Consumer Services | Personal Care |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Ohio since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Design Patterns programming
- Get your questions answered by easy to follow, organized Design Patterns experts
- Get up to speed with vital Design Patterns programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…