Java Programming Training Classes in Hoffman Estates, Illinois
Training Suggestions from the Experts

An Experienced Java developer must know
... everything or so it can seem. A solid grasp and knowledge of Object Oriented Programming constructs such as inheritance, polymorphism, interfaces and reflection are essential. Next in line is the knowldge to be able to import/export file data, running SQL queries, using regular expressions and, possibly, knowing how to write multi-threaded code and make socket connections. A class that addresses most of these topics is: Fast Track to Java 11 and OO Development.
For the more daring Java enthusiast and especially for those looking to become professional Java developers, knowledge of the Spring Framework is expected. A perfect class for this is: Fast Track to Spring Framework and Spring MVC/Rest. Not only does this course provide students with a great introduction to spring, it goes beyond the basics with a solid delve into Spring and web development.
Another consideration is learning JBoss aka Wildfly, the free Application Server from RedHat. JBoss has become the workhorse of most Java EE applications. Add to that a class on Tomcat, the defacto servlet engine, and the student can be considered 'ready' for employment.
Call for Details: 303.377.6176
Learn Java Programming in Hoffman Estates, Illinois and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Java Programming related training offerings in Hoffman Estates, Illinois: Java Programming Training
Java Programming Training Catalog
subcategories
JBoss Administration Classes
JUnit, TDD, CPTC, Web Penetration Classes
Java Enterprise Edition Classes
Java Programming Classes
Spring Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
What is computer crime? Computer crime, often called “cyber crime” is any type of illegal activity that takes place on a computer with a network. Oftentimes, when you think of computer crime, you might picture a home user downloading a virus that wipes out his hard drive or spyware that hijacks her system for the purposes of spying.
Computer crimes can also affect businesses too and they do, sometimes with devastating results. For example, in 2012, the IRS paid a whopping 5.2 billion dollars in tax refunds to identity thieves!
Protect your business and improve your bottom line by staying one step ahead of the cybercriminals.
5 Common Computer Crimes
If you’re interested in building modern websites or applications which use ASP, XML, or mobile technology, you’ve heard of Visual Studio .NET. It is one of the more popular suites of development tools available to aspiring programmers, as it consolidates several different tools and languages into the same development environment, which helps in turn to integrate this code across development languages. Here are three important benefits to using the visual studio suite:
· Use of Visual J# - This development tool is specifically oriented towards people who already are familiar with basic Java syntax, and is designed for use by those people to build apps or services which will then run on the Microsoft .NET Framework. This is useful because it fully supports Microsoft Extensions, among other reasons. Visual J# was developed completely independently by Microsoft.
· Utility for Smart Devices – Another huge benefit of using visual studio .NET is the ability to immediately integrate your programming efforts with deployment across a variety of smart devices. PDAs, smartphones, Pocket PCs, and any device which has a limited amount of resources all require a compact framework for the programming of applications it is designed to run.
· XML Web Usage and Support – Because XML services aren’t married to any particular technology or programming language, they can be accessed by any system, and this broad-based utility has made the services increasingly popular. Visual Studio .NET takes advantage of this by fully integrating with XML services, including the ability to create and edit them from scratch.
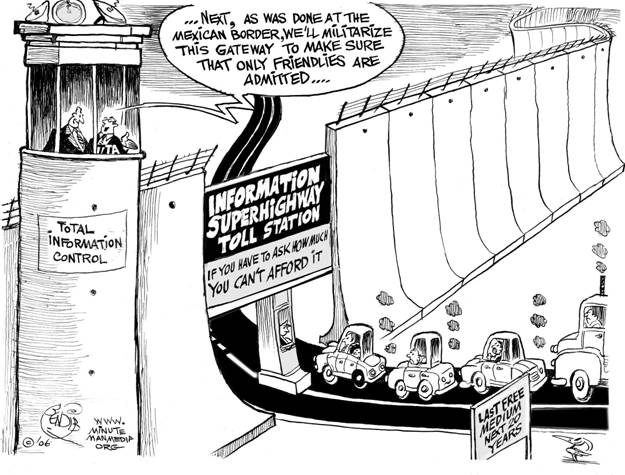
Net Neutrality
You may have heard about net neutrality over the years. Recently, the concept has gone through some changes, and many would consider its underlying principles to be in danger of corruption or dissolution. However, the technical nature of net neutrality ethics makes it difficult to understand for the layperson. Read on, and the central themes and controversies surrounding the principle will be outlined and explained for your convenience.
The Theme
This section of our beginning python training class always stumps students. Firstly, because they need to know the difference between a function and a method. Secondly, they need to understand object oriented programming concepts. Thirdly, they need to realize that python has three types of methods. Then they need to know how to use each method, which means they need to know the purpose of each method type. Then they have to understand mutable versus non-mutable types. The list goes on. As part of our python tutorial, I hope to shed some light on this confusing topic.
To begin, the difference between a function and a method in python is that a method is defined within a class. Here is an illustration:
#function def greeting(): print "Hello, I hope you're having a great day!" class HSGPrinter(object): #method def greeting(self): print "Hello, I hope you're having a great day!"
As should be obvious, the second definition of greeting is encapsulated within the HSGPrinter class and is , therefore, refered to as a method.
The astute reader will notice that the greeting method contains one parameter named self. For those who know C++ , Java or C#, self is equivalent to this i.e. it is a reference to the invoking object:
Tech Life in Illinois
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Illinois since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Java Programming programming
- Get your questions answered by easy to follow, organized Java Programming experts
- Get up to speed with vital Java Programming programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
