SharePoint Training Classes in Rochester, New York
Learn SharePoint in Rochester, NewYork and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current SharePoint related training offerings in Rochester, New York: SharePoint Training
SharePoint Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
 With the rise of the smart phone, many people who have long seen themselves as non-gamers have began to download and play to occupy themselves throughout the day. If you're a game developer who has a history of writing your code in C#, then perhaps this still emerging market is something you should consider taking advantage of. This, however, will require the familiarization with other programming languages.
With the rise of the smart phone, many people who have long seen themselves as non-gamers have began to download and play to occupy themselves throughout the day. If you're a game developer who has a history of writing your code in C#, then perhaps this still emerging market is something you should consider taking advantage of. This, however, will require the familiarization with other programming languages.
One option for moving away from the C# language is to learn Java. Java is the programming used for apps on the android platform, billions of phones run on this programming language.
If you want to break into the android market, then learning Java is an absolute must.
There are both some pros and some cons to learning java. Firstly, if you already know C# or other languages and understand how they work, then java will be relatively easy to learn due to having similar, but quite simplified, syntax to C-based languages, the class library is large and standardized, but also very well written, and you might find that it will improve the performance and portability of your creations. Not to mention, learning java opens you up to the entirety of the android app and game market, a very large and still growing market that would otherwise stay closed off to you. That's too much ad and sale money to risk missing out on.
The few cons that come with learning the language is that, when coming from other languages, the syntax may take some getting used to. This is true for most languages. The other problem is that you must be careful with the specifics of how you write your code. While java can be written in a very streamlined fashion, it's also possible to write working, but bulky, code that will slow down your programs. Practice makes perfect, and the knowledge to avoid such pitfalls within the language.
If you wish to develop for the iOS on the other hand, knowledge of Objective C is required. The most compelling reason to learn Objective C is the market that it will open you up to. According to the website AndroidAuthority.com, in the article "Google play vs. Apple app store", users of iPhones and other iOS devices are much more likely to spend money on apps rather than downloading free ones.
Though learning Objective C might be a far jump from someone who currently writes in C#, it's certainly learn-able with a little bit of practice.
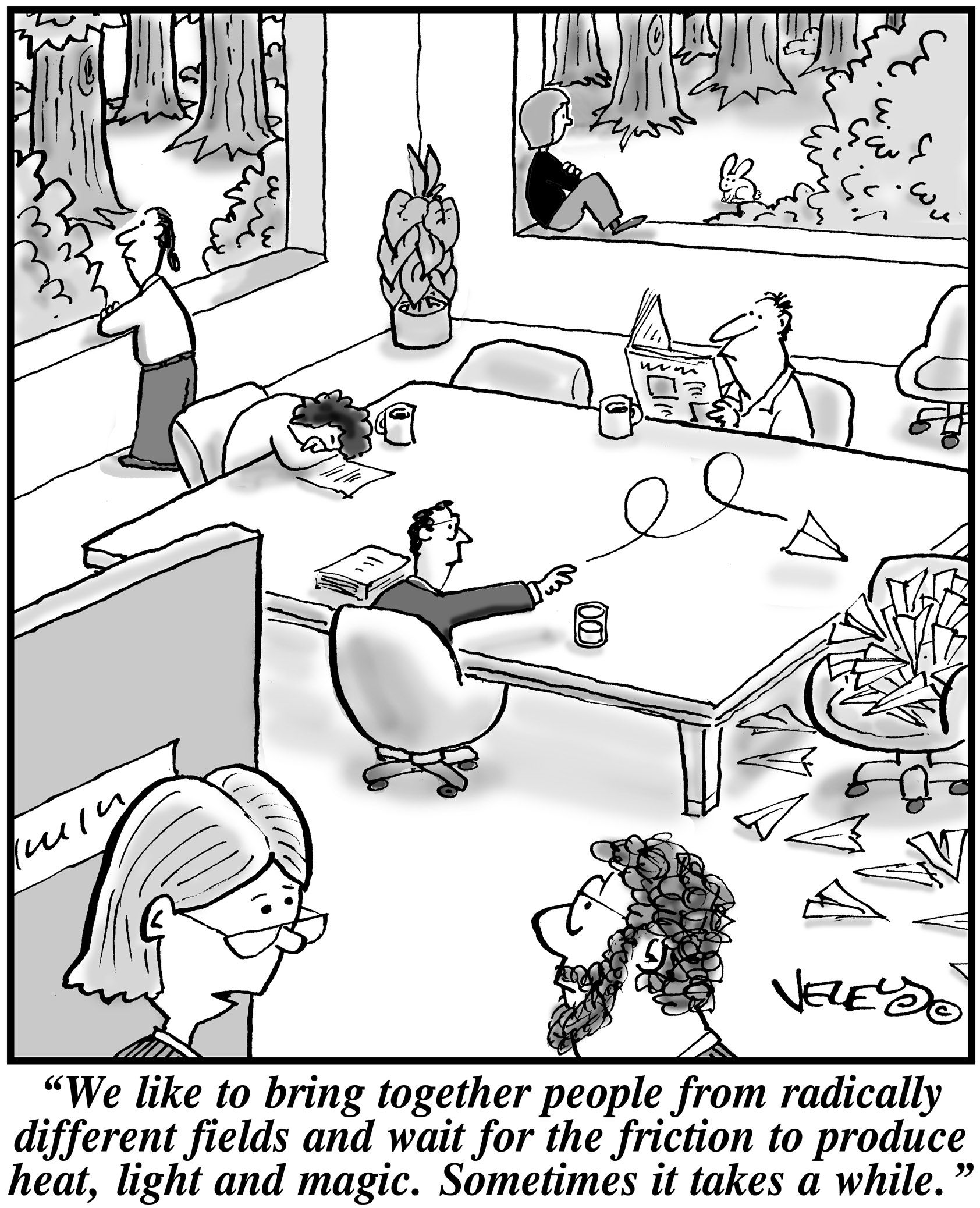
What are a few unique pieces of career advice that nobody ever mentions?
Good non-programmer jobs for people with software developer experience
 When it comes to running a start up, leaders need to make sure that their key players are motivated. This has been seen with many companies. Back in the 1970's it was found with the inspiration and diligence of the late Daniel Nigro when he formed Kleer-Fax. More recently it was seen in David Khasidy, the founder and recently retired president of SunRay Power Management, the most dynamic green energy leader in the US today.
When it comes to running a start up, leaders need to make sure that their key players are motivated. This has been seen with many companies. Back in the 1970's it was found with the inspiration and diligence of the late Daniel Nigro when he formed Kleer-Fax. More recently it was seen in David Khasidy, the founder and recently retired president of SunRay Power Management, the most dynamic green energy leader in the US today.
The question is, what is it that great leaders like David Khasidy and Daniel Nigro do that make the difference? How do the most vulnerable companies (start ups) break the mold and become a part of our everyday lives?
It starts with their mission and vision.
Create a Strong Mission and Vision
There are many reasons why start ups fail. For one, they usually lack the capital to last through the lean times. Secondly, they often don't have the tolerance for setbacks that occur. Lastly, they do not have a long-term plan, also called a mission.
When a business has a strong mission, the team knows it and their focus toward their work and service to others within and without the company reflects that. To complement that, the shorter term vision of the company needs to be present as well.
This can even be seen in sole proprietorships with no employees, such as when Brian Pascale started his law practice. His vision was to find justice for his clients while his mission was to build upon a career that had already set precedents in the area of tort law.
As his practice has grown, new staff members can sense the vision and mission he exudes.
Encourage Ownership of Projects and Processes
Start ups need to inspire and motivate their employees because they need to know that they are not only a part of something important, but that their contributions mean something.
What won't happen if they are not there? What contribution do they make, and what are the consequences of them not fulfilling their part of the work?
By encouraging ownership in projects, team members can find that the work they are doing is not only important for the organization, but that they are going to be a big part of what makes it happen. The alternative is that they feel replaceable.
Offer Incentives That Keep the Company Competitive
When team members embrace the mission and vision of the company, and then take ownership for the company's success, they are going to need to be justly rewarded.
This could include flexible schedules (for those who don't need a stringent one), use of an account at a nearby takeout place, or even the potential for ownership as a result of a vesting program.
The incentive everyone is looking for more immediately, though, is cash. When the company takes in more revenue as a result of the efforts of those on the team, rewarding them can go a long way not only in making them feel appreciated, but in encouraging them to bring in more business.
Members of a start up team are usually very talented, and commonly underpaid. However, if they believe they are going somewhere, it will make a big difference.
Related:
Good non-programmer jobs for people with software developer experience
It is said that spoken languages shape thoughts by their inclusion and exclusion of concepts, and by structuring them in different ways. Similarly, programming languages shape solutions by making some tasks easier and others less aesthetic. Using F# instead of C# reshapes software projects in ways that prefer certain development styles and outcomes, changing what is possible and how it is achieved.
F# is a functional language from Microsoft's research division. While once relegated to the land of impractical academia, the principles espoused by functional programming are beginning to garner mainstream appeal.
As its name implies, functions are first-class citizens in functional programming. Blocks of code can be stored in variables, passed to other functions, and infinitely composed into higher-order functions, encouraging cleaner abstractions and easier testing. While it has long been possible to store and pass code, F#'s clean syntax for higher-order functions encourages them as a solution to any problem seeking an abstraction.
F# also encourages immutability. Instead of maintaining state in variables, functional programming with F# models programs as a series of functions converting inputs to outputs. While this introduces complications for those used to imperative styles, the benefits of immutability mesh well with many current developments best practices.
For instance, if functions are pure, handling only immutable data and exhibiting no side effects, then testing is vastly simplified. It is very easy to test that a specific block of code always returns the same value given the same inputs, and by modeling code as a series of immutable functions, it becomes possible to gain a deep and highly precise set of guarantees that software will behave exactly as written.
Further, if execution flow is exclusively a matter of routing function inputs to outputs, then concurrency is vastly simplified. By shifting away from mutable state to immutable functions, the need for locks and semaphores is vastly reduced if not entirely eliminated, and multi-processor development is almost effortless in many cases.
Type inference is another powerful feature of many functional languages. It is often unnecessary to specify argument and return types, since any modern compiler can infer them automatically. F# brings this feature to most areas of the language, making F# feel less like a statically-typed language and more like Ruby or Python. F# also eliminates noise like braces, explicit returns, and other bits of ceremony that make languages feel cumbersome.
Functional programming with F# makes it possible to write concise, easily testable code that is simpler to parallelize and reason about. However, strict functional styles often require imperative developers to learn new ways of thinking that are not as intuitive. Fortunately, F# makes it possible to incrementally change habits over time. Thanks to its hybrid object-oriented and functional nature, and its clean interoperability with the .net platform, F# developers can gradually shift to a more functional mindset while still using the algorithms and libraries with which they are most familiar.
Related F# Resources:
Tech Life in New York
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| NYSE Euronext, Inc. | New York | Financial Services | Securities Agents and Brokers |
| Anderson Instrument Company Inc. | Fultonville | Manufacturing | Tools, Hardware and Light Machinery |
| News Corporation | New York | Media and Entertainment | Radio and Television Broadcasting |
| Philip Morris International Inc | New York | Manufacturing | Manufacturing Other |
| Loews Corporation | New York | Travel, Recreation and Leisure | Hotels, Motels and Lodging |
| The Guardian Life Insurance Company of America | New York | Financial Services | Insurance and Risk Management |
| Jarden Corporation | Rye | Manufacturing | Manufacturing Other |
| Ralph Lauren Corporation | New York | Retail | Clothing and Shoes Stores |
| Icahn Enterprises, LP | New York | Financial Services | Investment Banking and Venture Capital |
| Viacom Inc. | New York | Media and Entertainment | Media and Entertainment Other |
| Omnicom Group Inc. | New York | Business Services | Advertising, Marketing and PR |
| Henry Schein, Inc. | Melville | Healthcare, Pharmaceuticals and Biotech | Medical Supplies and Equipment |
| Pfizer Incorporated | New York | Healthcare, Pharmaceuticals and Biotech | Pharmaceuticals |
| Eastman Kodak Company | Rochester | Computers and Electronics | Audio, Video and Photography |
| Assurant Inc. | New York | Business Services | Data and Records Management |
| PepsiCo, Inc. | Purchase | Manufacturing | Nonalcoholic Beverages |
| Foot Locker, Inc. | New York | Retail | Department Stores |
| Barnes and Noble, Inc. | New York | Retail | Sporting Goods, Hobby, Book, and Music Stores |
| Alcoa | New York | Manufacturing | Metals Manufacturing |
| The Estee Lauder Companies Inc. | New York | Healthcare, Pharmaceuticals and Biotech | Personal Health Care Products |
| Avon Products, Inc. | New York | Healthcare, Pharmaceuticals and Biotech | Personal Health Care Products |
| The Bank of New York Mellon Corporation | New York | Financial Services | Banks |
| Marsh and McLennan Companies | New York | Financial Services | Insurance and Risk Management |
| Corning Incorporated | Corning | Manufacturing | Concrete, Glass, and Building Materials |
| CBS Corporation | New York | Media and Entertainment | Radio and Television Broadcasting |
| Bristol Myers Squibb Company | New York | Healthcare, Pharmaceuticals and Biotech | Biotechnology |
| Citigroup Incorporated | New York | Financial Services | Banks |
| Goldman Sachs | New York | Financial Services | Personal Financial Planning and Private Banking |
| American International Group (AIG) | New York | Financial Services | Insurance and Risk Management |
| Interpublic Group of Companies, Inc. | New York | Business Services | Advertising, Marketing and PR |
| BlackRock, Inc. | New York | Financial Services | Securities Agents and Brokers |
| MetLife Inc. | New York | Financial Services | Insurance and Risk Management |
| Consolidated Edison Company Of New York, Inc. | New York | Energy and Utilities | Gas and Electric Utilities |
| Time Warner Cable | New York | Telecommunications | Cable Television Providers |
| Morgan Stanley | New York | Financial Services | Investment Banking and Venture Capital |
| American Express Company | New York | Financial Services | Credit Cards and Related Services |
| International Business Machines Corporation | Armonk | Computers and Electronics | Computers, Parts and Repair |
| TIAA-CREF | New York | Financial Services | Securities Agents and Brokers |
| JPMorgan Chase and Co. | New York | Financial Services | Investment Banking and Venture Capital |
| The McGraw-Hill Companies, Inc. | New York | Media and Entertainment | Newspapers, Books and Periodicals |
| L-3 Communications Inc. | New York | Manufacturing | Aerospace and Defense |
| Colgate-Palmolive Company | New York | Consumer Services | Personal Care |
| New York Life Insurance Company | New York | Financial Services | Insurance and Risk Management |
| Time Warner Inc. | New York | Media and Entertainment | Media and Entertainment Other |
| Cablevision Systems Corp. | Bethpage | Media and Entertainment | Radio and Television Broadcasting |
| CA Technologies, Inc. | Islandia | Software and Internet | Software |
| Verizon Communications Inc. | New York | Telecommunications | Telephone Service Providers and Carriers |
| Hess Corporation | New York | Energy and Utilities | Gasoline and Oil Refineries |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in New York since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about SharePoint programming
- Get your questions answered by easy to follow, organized SharePoint experts
- Get up to speed with vital SharePoint programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
