C# Programming Training Classes in Lewisville, Texas
Learn C# Programming in Lewisville, Texas and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current C# Programming related training offerings in Lewisville, Texas: C# Programming Training
C# Programming Training Catalog
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - Linux Troubleshooting
1 June, 2026 - 5 June, 2026 - Docker
27 May, 2026 - 29 May, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
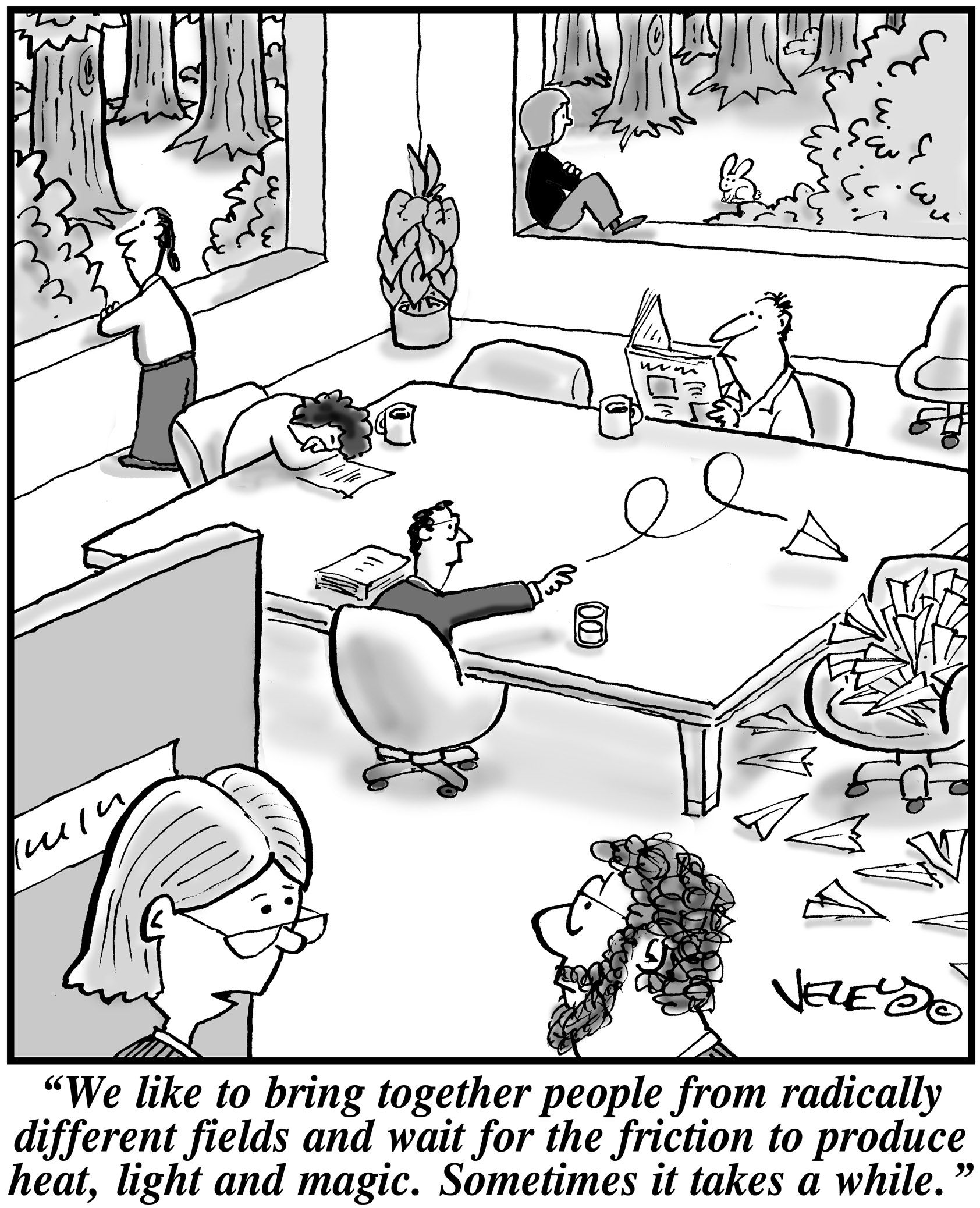 When it comes to running a start up, leaders need to make sure that their key players are motivated. This has been seen with many companies. Back in the 1970's it was found with the inspiration and diligence of the late Daniel Nigro when he formed Kleer-Fax. More recently it was seen in David Khasidy, the founder and recently retired president of SunRay Power Management, the most dynamic green energy leader in the US today.
When it comes to running a start up, leaders need to make sure that their key players are motivated. This has been seen with many companies. Back in the 1970's it was found with the inspiration and diligence of the late Daniel Nigro when he formed Kleer-Fax. More recently it was seen in David Khasidy, the founder and recently retired president of SunRay Power Management, the most dynamic green energy leader in the US today.
The question is, what is it that great leaders like David Khasidy and Daniel Nigro do that make the difference? How do the most vulnerable companies (start ups) break the mold and become a part of our everyday lives?
It starts with their mission and vision.
Create a Strong Mission and Vision
There are many reasons why start ups fail. For one, they usually lack the capital to last through the lean times. Secondly, they often don't have the tolerance for setbacks that occur. Lastly, they do not have a long-term plan, also called a mission.
When a business has a strong mission, the team knows it and their focus toward their work and service to others within and without the company reflects that. To complement that, the shorter term vision of the company needs to be present as well.
This can even be seen in sole proprietorships with no employees, such as when Brian Pascale started his law practice. His vision was to find justice for his clients while his mission was to build upon a career that had already set precedents in the area of tort law.
As his practice has grown, new staff members can sense the vision and mission he exudes.
Encourage Ownership of Projects and Processes
Start ups need to inspire and motivate their employees because they need to know that they are not only a part of something important, but that their contributions mean something.
What won't happen if they are not there? What contribution do they make, and what are the consequences of them not fulfilling their part of the work?
By encouraging ownership in projects, team members can find that the work they are doing is not only important for the organization, but that they are going to be a big part of what makes it happen. The alternative is that they feel replaceable.
Offer Incentives That Keep the Company Competitive
When team members embrace the mission and vision of the company, and then take ownership for the company's success, they are going to need to be justly rewarded.
This could include flexible schedules (for those who don't need a stringent one), use of an account at a nearby takeout place, or even the potential for ownership as a result of a vesting program.
The incentive everyone is looking for more immediately, though, is cash. When the company takes in more revenue as a result of the efforts of those on the team, rewarding them can go a long way not only in making them feel appreciated, but in encouraging them to bring in more business.
Members of a start up team are usually very talented, and commonly underpaid. However, if they believe they are going somewhere, it will make a big difference.
Related:
Good non-programmer jobs for people with software developer experience
A career in the field of software development remains immensely popular due to various factors. Chief among them of course is the higher compensation and lucrative pay scale in the IT industry when compared to other career options. In addition, the flexibility of work hours and the sheer sense of achievement experienced by one while creating new programs are unsurpassed by any other job.
Popularity and reach of Software Programs
Software programming has become a quintessential part of our day to day life, right from the smartphones in your pocket, to video gaming, and everything in between. The opportunities in this field are truly astounding. The niches for specializing are also diverse, from creating operating systems, to mobile app development, or web app development to name a few.
There are various ways in which you can distinguish yourself in the market for the much coveted title of software programmer. Here, we focus on some of them.
 One of the biggest challenges faced by senior IT professionals in organizations is the choice of the right software vendor. In the highly competitive enterprise software industry, there are lot of vendors who claim to offer the best software for the problem and it can be really daunting to narrow down the best choice. Additionally, enterprise software costs can often run into millions of dollars thereby leaving very little margin of error. The real cost of choosing a wrong software can often result into losses much more than the cost of the software itself as highlighted by software disasters experienced by leading companies like HP, Nike etc. In such a scenario, senior IT professionals despite years of expertise can find it very difficult to choose the right business software vendor for their organization.
One of the biggest challenges faced by senior IT professionals in organizations is the choice of the right software vendor. In the highly competitive enterprise software industry, there are lot of vendors who claim to offer the best software for the problem and it can be really daunting to narrow down the best choice. Additionally, enterprise software costs can often run into millions of dollars thereby leaving very little margin of error. The real cost of choosing a wrong software can often result into losses much more than the cost of the software itself as highlighted by software disasters experienced by leading companies like HP, Nike etc. In such a scenario, senior IT professionals despite years of expertise can find it very difficult to choose the right business software vendor for their organization.
Here are some of the proven ways of short-listing and selecting the right business software vendor for your organization,
· Understand and Define The Exact Need First: Before embarking on a journey to select the software vendor, it is critical to understand and define the exact problem you want the software to solve. The paramount question to be asked is what business objective does the software need to solve. Is the software required to “reduce costs” or is it to “improve productivity”? Extracting and defining this fundamental question is the bare minimum but necessary step to go searching for the right vendor. It will then form the basis of comparing multiple vendors on this very need that your organization has and will help drive the selection process going forward. The detailed approach involves creating a set of parameters that the software needs to meet in order to be considered. In fact, consider categorizing these parameters further in “must-haves”, “good to have” etc. which will help you assign relevant weights to these parameter and how the software’s fare on each of these parameters
· Building The List of Vendors Who Meet The Need: Once you have defined your need and distilled that need into various parameters, it’s time to built the list of vendors who you think will meet the need. This is akin to a lead generation model wherein you want to identify a large enough pool and then filters your list down to the best ones. There are multiple ways of building a list of vendors and more often than not, you must use a combination of these methods to build a good enough list.
o Use Industry Reports: We discussed the IT intelligence offered by leading industry firms Gartner and Forrester in How To Keep On Top Of Latest Trends In Information Technology. These firms based on their access to leading software vendors and CIO network publish vendor comparison research reports across specific verticals as well as specific technologies. Gartner’s Magic Quadrant and Forrester’s Wave are a very good starting point to get an insight into the best software vendors. For example, if you were looking for a CRM solution, you could look for Gartner’s Magic Quadrant for CRM and look at the vendors that make the list. These reports can be pricey but well worth the money if you are going to invest hundreds of thousands in the software. Having said that, you don’t have to trust these report blindly because how these firms define the best software may not match how you define the best software for your organization
o Competitive Intelligence: If you are a smart professional, you are already keeping tabs of your competition. Chances are that if you are a big organization, you might see a Press Release either from your competitor or their vendor announcing the implementation of new software. Extrapolate that across 5-10 key competitors of yours and you might discover the vendors that your competitors are choosing. This gives you a good indicator that the vendors used by your competitors must be offering something right.
Due to the advancements in technology, teens and adults alike can now partake in virtual worlds thanks to video games. Video games are enjoyed as a hobby all over the globe, but some gamers have made it their career with help from the ever-growing e-sport community. This is an inside look at the professional level of gaming from an ex-MLG participant, and what I remember going through when starting to play video games at an elite level.
One of the premiere and most popular leagues within the United States happens to be Major League Gaming or MLG for short. This is a league that usually involves more of the most recent games out, and they create circuits for each major title and its subsequent releases. Two of the most major game circuits within the MLG league were the Halo series and the Call of Duty series, both which happened to be first person shooters (FPS). There were a potential hundred or so teams within each circuit, but much like other competitions, the circuits were ran with winner’s brackets and losers brackets. This means that out of all the teams that would show up to MLG events, about the top eight of each bracket would really be known as the "elite" players. I personally played in the Gears of War circuit at venues like MLG Raleigh and MLG Toronto, and we had very few teams compared to Call of Duty and Halo. The amount of participants at each event usually varies in each circuit based on the popularity of the game being played.
When you win tournaments, the payouts are split between the team members. This means that looking at playing in the MLG for a life career is an ill-advised move. The cost to get to events and buy team passes usually negates the prizes you win most of the time, considering by the time that the prize money is split you are left with about $800 in a popular circuit (Like Call of Duty). The payouts are usually only high in special and certain occasions, one for example being the million dollar showdown that Infinity Ward hosted for Call of Duty: Modern Warfare 3 a couple years back. The way that players that make professional gaming their career get the big money now is by being sponsored by the big companies that back the league like Red Bull and Hot Pockets. MLG players like "Walshy" and "FeaR Moho" were sponsored early on in the league and were able to make a living off of the games they played. I would imagine them getting around $60K in a good year off of sponsors alone. I would go even as far as to say that if you do not have a sponsor in e-sports, you will not be financially successful in the career.
Being an MLG gamer requires passion and understanding for the games. If you just want to make money, then you are better off working at McDonalds.
How to Keep a Start Up Team Motivated?
What People Should Know Before Getting Rid of Old Tech Stuff
Surprising Ways Viruses, Malware, Etc. are Infecting Computers
Tech Life in Texas
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Dr Pepper Snapple Group | Plano | Manufacturing | Nonalcoholic Beverages |
| Western Refining, Inc. | El Paso | Energy and Utilities | Gasoline and Oil Refineries |
| Frontier Oil Corporation | Dallas | Manufacturing | Chemicals and Petrochemicals |
| ConocoPhillips | Houston | Energy and Utilities | Gasoline and Oil Refineries |
| Dell Inc | Round Rock | Computers and Electronics | Computers, Parts and Repair |
| Enbridge Energy Partners, L.P. | Houston | Transportation and Storage | Transportation & Storage Other |
| GameStop Corp. | Grapevine | Retail | Retail Other |
| Fluor Corporation | Irving | Business Services | Management Consulting |
| Kimberly-Clark Corporation | Irving | Manufacturing | Paper and Paper Products |
| Exxon Mobil Corporation | Irving | Energy and Utilities | Gasoline and Oil Refineries |
| Plains All American Pipeline, L.P. | Houston | Energy and Utilities | Gasoline and Oil Refineries |
| Cameron International Corporation | Houston | Energy and Utilities | Energy and Utilities Other |
| Celanese Corporation | Irving | Manufacturing | Chemicals and Petrochemicals |
| HollyFrontier Corporation | Dallas | Energy and Utilities | Gasoline and Oil Refineries |
| Kinder Morgan, Inc. | Houston | Energy and Utilities | Gas and Electric Utilities |
| Marathon Oil Corporation | Houston | Energy and Utilities | Gasoline and Oil Refineries |
| United Services Automobile Association | San Antonio | Financial Services | Personal Financial Planning and Private Banking |
| J. C. Penney Company, Inc. | Plano | Retail | Department Stores |
| Energy Transfer Partners, L.P. | Dallas | Energy and Utilities | Energy and Utilities Other |
| Atmos Energy Corporation | Dallas | Energy and Utilities | Alternative Energy Sources |
| National Oilwell Varco Inc. | Houston | Manufacturing | Manufacturing Other |
| Tesoro Corporation | San Antonio | Manufacturing | Chemicals and Petrochemicals |
| Halliburton Company | Houston | Energy and Utilities | Energy and Utilities Other |
| Flowserve Corporation | Irving | Manufacturing | Tools, Hardware and Light Machinery |
| Commercial Metals Company | Irving | Manufacturing | Metals Manufacturing |
| EOG Resources, Inc. | Houston | Energy and Utilities | Gasoline and Oil Refineries |
| Whole Foods Market, Inc. | Austin | Retail | Grocery and Specialty Food Stores |
| Waste Management, Inc. | Houston | Energy and Utilities | Waste Management and Recycling |
| CenterPoint Energy, Inc. | Houston | Energy and Utilities | Gas and Electric Utilities |
| Valero Energy Corporation | San Antonio | Manufacturing | Chemicals and Petrochemicals |
| FMC Technologies, Inc. | Houston | Energy and Utilities | Alternative Energy Sources |
| Calpine Corporation | Houston | Energy and Utilities | Gas and Electric Utilities |
| Texas Instruments Incorporated | Dallas | Computers and Electronics | Semiconductor and Microchip Manufacturing |
| SYSCO Corporation | Houston | Wholesale and Distribution | Grocery and Food Wholesalers |
| BNSF Railway Company | Fort Worth | Transportation and Storage | Freight Hauling (Rail and Truck) |
| Affiliated Computer Services, Incorporated (ACS), a Xerox Company | Dallas | Software and Internet | E-commerce and Internet Businesses |
| Tenet Healthcare Corporation | Dallas | Healthcare, Pharmaceuticals and Biotech | Hospitals |
| XTO Energy Inc. | Fort Worth | Energy and Utilities | Gasoline and Oil Refineries |
| Group 1 Automotive | Houston | Retail | Automobile Dealers |
| ATandT | Dallas | Telecommunications | Telephone Service Providers and Carriers |
| Anadarko Petroleum Corporation | Spring | Energy and Utilities | Gasoline and Oil Refineries |
| Apache Corporation | Houston | Energy and Utilities | Gasoline and Oil Refineries |
| Dean Foods Company | Dallas | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
| American Airlines | Fort Worth | Travel, Recreation and Leisure | Passenger Airlines |
| Baker Hughes Incorporated | Houston | Energy and Utilities | Gasoline and Oil Refineries |
| Continental Airlines, Inc. | Houston | Travel, Recreation and Leisure | Passenger Airlines |
| RadioShack Corporation | Fort Worth | Computers and Electronics | Consumer Electronics, Parts and Repair |
| KBR, Inc. | Houston | Government | International Bodies and Organizations |
| Spectra Energy Partners, L.P. | Houston | Energy and Utilities | Gas and Electric Utilities |
| Energy Future Holdings | Dallas | Energy and Utilities | Energy and Utilities Other |
| Southwest Airlines Corporation | Dallas | Transportation and Storage | Air Couriers and Cargo Services |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Texas since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about C# Programming programming
- Get your questions answered by easy to follow, organized C# Programming experts
- Get up to speed with vital C# Programming programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…

