JUnit, TDD, CPTC, Web Penetration Training Classes in Aurora, Colorado
Learn JUnit, TDD, CPTC, Web Penetration in Aurora, Colorado and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current JUnit, TDD, CPTC, Web Penetration related training offerings in Aurora, Colorado: JUnit, TDD, CPTC, Web Penetration Training
JUnit, TDD, CPTC, Web Penetration Training Catalog
subcategories
Android and iPhone Programming Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
 Not getting any hits on your dating profile? It doesn’t mean you’re a loser. There are literally millions of computer dating profiles out there and dozens of free and paid websites to find a date. A dating profile is kind of like a resume for your personal life. To succeed, you have to learn a few tricks to stand out.
Not getting any hits on your dating profile? It doesn’t mean you’re a loser. There are literally millions of computer dating profiles out there and dozens of free and paid websites to find a date. A dating profile is kind of like a resume for your personal life. To succeed, you have to learn a few tricks to stand out.
Tips to Improve Your Computer Dating Profile
1. Make a Good First Impression
Filling out an online dating profile can be a daunting task. When you’re faced with all that blank space to write about yourself, it gets intimidating. The best way to improve your computer dating odds is to make a good first impression. Start with a good opening line such as a favorite quote or a personal motto you can easy build on.
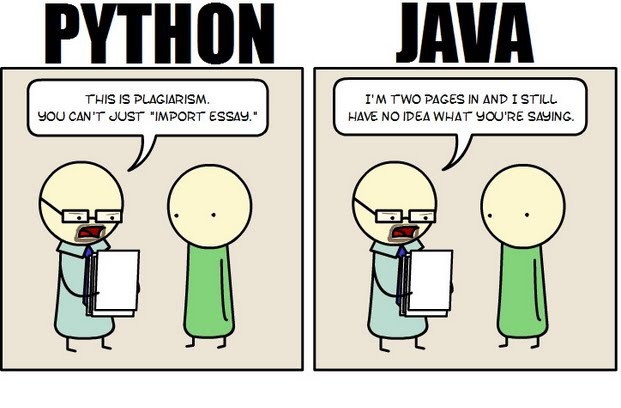 Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
First, Java is a static typed language while Python is dynamically typed. Static typed languages require that each variable name must be tied to both a type and an object. Dynamically typed languages only require that a variable name only gets bound to an object. Immediately, this puts Python ahead of the game in terms of productivity since a static typed language requires several elements and can make errors in coding more likely.
Python uses a concise language while Java uses verbose language. Concise language, as the name suggests, gets straight to the point without extra words. Removing additional syntax can greatly reduce the amount of time required to program. A simple call in Java, such as the ever notorious "Hello, World" requires three several lines of coding while Python requires a single sentence. Java requires the use of checked exceptions. If the exceptions are not caught or thrown out then the code fails to compile. In terms of language, Python certainly has surpassed Java in terms of brevity.
Additionally, while Java's string handling capabilities have improved they haven't yet matched the sophistication of Python's. Web applications rely upon fast load times and extraneous code can increase user wait time. Python optimizes code in ways that Java doesn't, and this can make Python a more efficient language. However, Java does run faster than Python and this can be a significant advantage for programmers using Java. When you factor in the need for a compiler for Java applications the speed factor cancels itself out leaving Python and Java at an impasse.
While a programmer will continue to argue for the language that makes it easiest based on the programmer's current level of knowledge, new software compiled with Python takes less time and provides a simplified coding language that reduces the chance for errors. When things go right, Java works well and there are no problems. However, when errors get introduced into the code, it can become extremely time consuming to locate and correct those errors. Python generally uses less code to begin with and makes it easier and more efficient to work with.
Ultimately, both languages have their own strengths and weaknesses. For creating simple applications, Python provides a simpler and more effective application. Larger applications can benefit from Java and the verbosity of the code actually makes it more compatible with future versions. Python code has been known to break with new releases. Ultimately, Python works best as a type of connecting language to conduct quick and dirty work that would be too intensive when using Java alone. In this sense, Java is a low-level implementation language. While both languages are continuing to develop, it's unlikely that one language will surpass the other for all programming needs in the near future.
Disruptive technologies such as hand-held devices, cloud computing and social media are rattling the foundations upon which traditional businesses are built. Enterprise customers have grown smarter at ensuring the latest technological trends work in their favor. Everyone is trying to zero in on their core competencies by employing commodity services to run their business.
Likewise, enterprise application vendors need to zero in on their core competencies and enhance more value to the businesses of their clientele by leveraging standards-based commodity services, such as IaaS and PaaS, provided by leaders in those segments (e.g. Amazon EC2, Google Cloud Platform etc.).
What else enterprises need to do is learn to adopt new and emerging technologies such as cloud, utility and social computing to build on them to penetrate new market avenues.
New small and medium-sized entrants into the market are constantly challenging enterprises given their ability to rapidly turnaround and address the requirements of the customers in a cost-effective manner. Additionally, these new advancements also affect how enterprises create, deploy, and manage solutions and applications. If you take the example of Force.com, for instance, you find that it’s a common war zone for enterprise application vendors to furnish SME markets with their applications, with the new entrants mostly having an edge.

If you're someone who's interested in computer programming, chances are you've considered pursuing a career in it. However, being a computer programmer is definitely not for everyone, as it takes some special characteristics to succeed as a computer programmer.
Good at Math
While you don't have to be a math genius in order to be a good computer programmer, being good at math really does help. In general, as long as you know your trigonometry and advanced high school algebra, you should be set for programming.
However, in a few instances, knowledge of more advanced math ends up being necessary. For example, for shader programming, you should be familiar with integration of multiple variables, matrix algebra, and basic differentiation. You will also require considerable math skills in order to program 3D.
Excellent Problem Solver
To be a successful computer programmer, you definitely need to be an excellent problem solver. It is vital for a computer programmer to break a problem down into small parts. They must then be able to decide the best way to approach individual pieces of the problem. Computer programmers also need to know how to anticipate and prevent potential problems. While problem-solving, they also need to keep in mind things like user experience and performance.
If you're not a good problem solver, knowing a particular language and syntax will be useless if you can't even identify the problem at hand. Therefore, excellent problem solving skills are a critical foundation for computer programming.
Patience
If you are not a patient person, you will quickly become very frustrated with computer programming. Problem-solving is not always easy and fast. In fact, it may take a very long time, especially if you're either inexperienced or working on an especially hard project.
Debugging after the coding process is also very frustrating and tedious. No matter how hard you try, you will always have bugs in your coding, and these bugs, while often easy to fix, tend to be very difficult to detect. Therefore, you will end up spending a lot of your time searching for bugs that take very little time to fix.
Well-Rounded Skills
Generally, computer programmers who are very skilled in one area tend to stick around longer than jack-of-all-trades, as specialized programmers are harder to replace with outsourcing than general programmers. Therefore, it will do you well to specialize in one area of computer programming.
However, while specializing is good, you should still know at least a little about everything, especially skills that relate to the area you specialize in. For example, if you're a core Java programmer, you should know about SQL programming and ideally a scripting language or some regular expressions.
As you can see, not everyone has what it takes to pursue computer programming as a career and succeed at it. In fact, just because you love to program doesn't mean it's a good career choice for you. However, if you feel that you possess all the characteristics listed above, then you should definitely consider computer programming as a career.
Tech Life in Colorado
| Company Name | City | Industry | Secondary Industry |
|---|---|---|---|
| Level 3 Communications, Inc | Broomfield | Telecommunications | Telecommunications Other |
| Liberty Global, Inc. | Englewood | Telecommunications | Video and Teleconferencing |
| Liberty Media Corporation | Englewood | Media and Entertainment | Media and Entertainment Other |
| Western Union Company | Englewood | Financial Services | Financial Services Other |
| Ball Corporation | Broomfield | Manufacturing | Metals Manufacturing |
| Pilgrim's Pride Corporation | Greeley | Manufacturing | Food and Dairy Product Manufacturing and Packaging |
| Molson Coors Brewing Company | Denver | Manufacturing | Alcoholic Beverages |
| DISH Network Corporation | Englewood | Media and Entertainment | Media and Entertainment Other |
| Arrow Electronics, Inc. | Englewood | Computers and Electronics | Networking Equipment and Systems |
| DaVita, Inc. | Denver | Healthcare, Pharmaceuticals and Biotech | Outpatient Care Centers |
| Blockbuster LLC | Englewood | Media and Entertainment | Media and Entertainment Other |
| CH2M HILL | Englewood | Energy and Utilities | Alternative Energy Sources |
| Newmont Mining Corporation | Greenwood Vlg | Agriculture and Mining | Mining and Quarrying |
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Colorado since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about JUnit, TDD, CPTC, Web Penetration programming
- Get your questions answered by easy to follow, organized JUnit, TDD, CPTC, Web Penetration experts
- Get up to speed with vital JUnit, TDD, CPTC, Web Penetration programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
