Linux Unix Training Classes in London United, Kingdom
Learn Linux Unix in London United, Kingdom and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Linux Unix related training offerings in London United, Kingdom: Linux Unix Training
View all Scheduled Linux Unix Training Classes
Linux Unix Training Catalog
subcategories
DevOps Classes
Foundations of Web Design & Web Authoring Classes
Java Programming Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- Linux Fundamentals
11 May, 2026 - 15 May, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - Docker
27 May, 2026 - 29 May, 2026 - Linux Troubleshooting
1 June, 2026 - 5 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
18 May, 2026 - 22 May, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
Being treated like a twelve year old at work by a Tasmanian-devil-manager and not sure what to do about it? It is simply a well-known fact that no one likes to be micro managed. Not only do they not like to be micro managed, but tend to quit for this very reason. Unfortunately the percentage of people leaving their jobs for this reason is higher that you would imagine. Recently, an employee retention report conducted by TINYpulse, an employee engagement firm, surveyed 400 full-time U.S. employees concluded that, "supervisors can make or break employee retention."
As companies mature, their ability to manage can be significant to their bottom line as employee morale, high staff turnover and the cost of training new employees can easily reduce productivity and consequently client satisfaction. In many cases, there is a thin line between effective managing and micro managing practices. Most managers avoid micro managing their employees. However, a decent percentage of them have yet to find effective ways to get the most of their co-workers. They trap themselves by disempowering people's ability to do their work when they hover over them and create an unpleasant working environment. This behavior may come in the form of incessant emailing, everything having to be done a certain way (their way), desk hovering, and a need to control every part of an enterprise, no matter how small.
Superimpose the micro manager into the popular practice of Agile-SCRUM methodology and you can imagine the creative ways they can monitor everything in a team, situation, or place. Although, not always a bad thing, excessive control, can lead to burnout of managers and teams alike. As predicted, agile project management has become increasingly popular in the last couple of decades in project planning, particularly in software development. Agile methodology when put into practice, especially in IT, can mean releasing faster functional software than with the traditional development methods. When done right, it enables users to get some of the business benefits of the new software faster as well as enabling the software team to get rapid feedback on the software's scope and direction.
Despite its advantages, most organizations have not been able to go “all agile” at once. Rather, some experiment with their own interpretation of agile when transitioning. A purist approach for instance, can lead to an unnecessarily high agile project failure, especially for those that rely on tight controls, rigid structures and cost-benefit analysis. As an example, a premature and rather rapid replacement of traditional development without fully understating the implications of the changeover process or job roles within the project results in failure for many organizations.
The iconic software company that is based in King County Washington has been getting almost universally slammed from it's recent Los Angeles press announcement about its entry into the hardware business with the convertible laptop/tablet known as Surface.
Certainly I can see the point that it is now competing with its hardware vendors/partners. Intel has done a good job in the arena creating 'reference designs' without competing with its partners.
There is another viewpoint which seems to be ignored. The cold facts are Microsoft is a public company. This puts Microsoft in a legal position of doing the most it can to return value to its shareholders. Failure to do so means somebody is going to jail.
Microsoft has a vision, which at the end of the day is, a certain way to get enough people to see enough value to hand over their money, to fulfill their fiduciary duty.
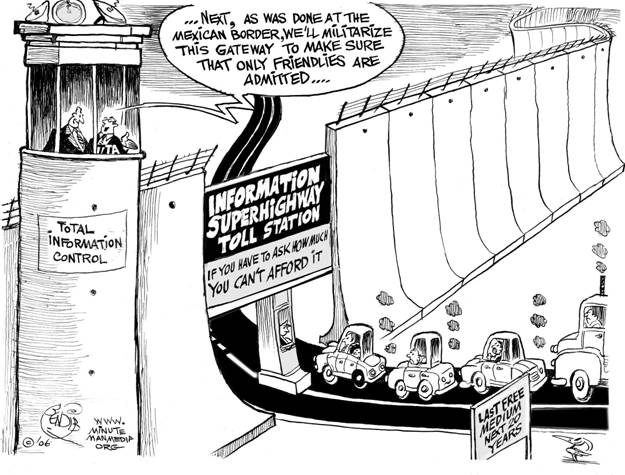
Net Neutrality
You may have heard about net neutrality over the years. Recently, the concept has gone through some changes, and many would consider its underlying principles to be in danger of corruption or dissolution. However, the technical nature of net neutrality ethics makes it difficult to understand for the layperson. Read on, and the central themes and controversies surrounding the principle will be outlined and explained for your convenience.
The Theme
Evolving technologies become fun due to the immense advantages and features they bring with them. Fighting change though is human and while we may initially resist such changes, it is always better to accept them to our advantage.
Switching to HTML 5 is one such change we need to be ready for and there are at least 8 reasons why we should be doing so which are explained later in the article.
Earlier HTML was mainly used only for Web content development. But with the arrival of HTML 5, there would be a radical shift in that it would be used more and more for the development of many of the client side applications as well. The advantages straight away are that CSS as well as JavaScript become free due to the open architecture environment. HTML 5 is also pretty light and has a much easier code to read, making it convenient for devices like smart phones and tablets running on batteries to use the applications.
The 8 reasons mentioned above are as under:
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Kingdom since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Linux Unix programming
- Get your questions answered by easy to follow, organized Linux Unix experts
- Get up to speed with vital Linux Unix programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…

