.NET Training Classes in Juneau, Alaska
Learn .NET in Juneau, Alaska and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current .NET related training offerings in Juneau, Alaska: .NET Training
.NET Training Catalog
subcategories
C# Programming Classes
Design Patterns Classes
F# Programming Classes
JUnit, TDD, CPTC, Web Penetration Classes
Microsoft Development Classes
Microsoft Office Classes
Microsoft Windows Server Classes
SharePoint Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight

Jeff Nelson, a former Googler and inventor of Chromebook says on Quora, “One habit I've clung to is writing small prototypes when I'm trying to learn new concepts.
For example, I'll sit down with a book or a web page, and over the course of a few hours, write 30 or 40 programs all of them only a few dozen lines long. Each program intended to demonstrate some simple concept. This prototyping makes it very easy to try out many concepts in a short period of time.”
Miguel Paraz, Software Engineering Student habit is to “keep a log in a text file or document on my work computer. Before trying to solve a problem, I write it down first. And then I describe the details as they happen.”
The RSS feed, which commonly stands for Really Simple Syndication, is an internet protocol that helps spread the availability of frequently published or updated Internet content.
RSS Benefits for an Internet Content Provider or Blogger
The use of an RSS feed saves immeasurable time for a content provider. When an interested person subscribes to an RSS feed, the owner of that feed now has a way to reach large numbers of people without having to resort to spamming techniques. The RSS feed also allows a content provider to send the requested topical information without specifically asking, every time, to those people who have subscribed. The content provider uses a program, written in XML code to make the information they post available to each person that has requested a subscription to that particular RSS feed.
RSS Benefits for the Average Internet User
The Internet grows larger by the minute. It is easy for a person to have information overload. The use of an RSS feed gives an individual more control over what information they see while on the Internet. It is also very useful for anyone that wants to stay up to date. Subscribing to the RSS feed for a topic of interest automatically provides the subscriber continued availability of the latest information on that topic. The Internet user relies on a small program called an RSS Feeder to gather the information on the RSS feeds to which they have subscribed.
Most browsers these days have built in RSS readers making that gathering the desired information easier than ever to accomplish. Joining an RSS feed is a very simple thing to accomplish.
RSS Benefits for Small Businesses
More and more Small Business owners are adapting targeted online marketing campaigns such as RSS Feeds in order to provide relevant content to new and existing customers. Maintaining web content such as: company news; contests; promotional events; related articles; notifications; product launches; directories; and newsletters are examples of ways of staying in touch with customers in any niche market. As search engines retrieve information from RSS Feeds and content is syndicated to other websites, chances of increased traffic are inevitable. For active websites, RSS feeds are invaluable tools for small business owners.
USA.gov Updates: News and Features
Search for RSS feeds (search topics)
Welcome to Google Reader (find and keep track of interesting stuff on the web.)
NPR public radio station (popular, news, program and topics RSS feeds)
RSS in Plain English (video)
10 Helpful Uses of RSS Feeds for Marketing
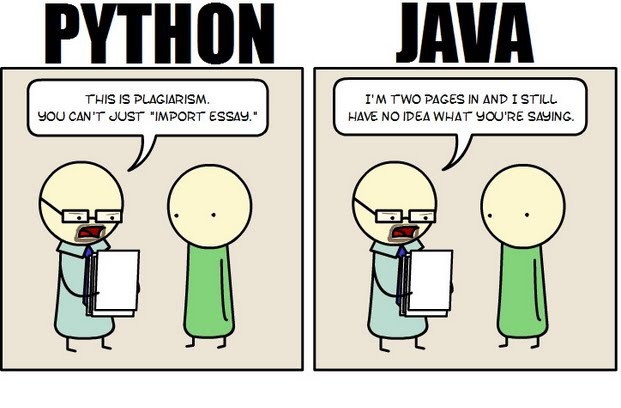 Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
First, Java is a static typed language while Python is dynamically typed. Static typed languages require that each variable name must be tied to both a type and an object. Dynamically typed languages only require that a variable name only gets bound to an object. Immediately, this puts Python ahead of the game in terms of productivity since a static typed language requires several elements and can make errors in coding more likely.
Python uses a concise language while Java uses verbose language. Concise language, as the name suggests, gets straight to the point without extra words. Removing additional syntax can greatly reduce the amount of time required to program. A simple call in Java, such as the ever notorious "Hello, World" requires three several lines of coding while Python requires a single sentence. Java requires the use of checked exceptions. If the exceptions are not caught or thrown out then the code fails to compile. In terms of language, Python certainly has surpassed Java in terms of brevity.
Additionally, while Java's string handling capabilities have improved they haven't yet matched the sophistication of Python's. Web applications rely upon fast load times and extraneous code can increase user wait time. Python optimizes code in ways that Java doesn't, and this can make Python a more efficient language. However, Java does run faster than Python and this can be a significant advantage for programmers using Java. When you factor in the need for a compiler for Java applications the speed factor cancels itself out leaving Python and Java at an impasse.
While a programmer will continue to argue for the language that makes it easiest based on the programmer's current level of knowledge, new software compiled with Python takes less time and provides a simplified coding language that reduces the chance for errors. When things go right, Java works well and there are no problems. However, when errors get introduced into the code, it can become extremely time consuming to locate and correct those errors. Python generally uses less code to begin with and makes it easier and more efficient to work with.
Ultimately, both languages have their own strengths and weaknesses. For creating simple applications, Python provides a simpler and more effective application. Larger applications can benefit from Java and the verbosity of the code actually makes it more compatible with future versions. Python code has been known to break with new releases. Ultimately, Python works best as a type of connecting language to conduct quick and dirty work that would be too intensive when using Java alone. In this sense, Java is a low-level implementation language. While both languages are continuing to develop, it's unlikely that one language will surpass the other for all programming needs in the near future.
It is hard not to wonder how current technology would have altered the events surrounding the tragic death of John F. Kennedy. On the afternoon of November 22, 1963, shots rang out in Dallas, TX, taking the life of JFK, one of the most beloved Americans. Given the same circumstances today, surely the advances in IT alone, would have drastically changed the outcome of that horrible day. Would the government have recognized that there was a viable threat looming over JFK? Would local and government agencies have been more prepared for a possible assassination attempt? Would the assortment of everyday communication devices assisted in the prevention of the assassination, not to mention, provided greater resources into the investigation? With all that the IT world has to offer today, how would it have altered the JFK tragedy?
As many conspiracy theories have rocked the foundation of the official story presented by government agencies, realization of the expansive nature of technology provides equal consideration as to how the event would have been changed had this technology been available during the time of the shooting. There were T.V. cameras, home 8mm recorders, even single shot-hand held cameras snapping away as the car caravan approached. Yet, there remains little documentation of the shooting and even less information pertaining to the precautions taken by officials prior to JFK's arrival. Theorists consider these possibilities along with how the world would have turned out had the great John F. Kennedynever been assassinated on that day.
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in Alaska since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about .NET programming
- Get your questions answered by easy to follow, organized .NET experts
- Get up to speed with vital .NET programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…

