Security Training Classes in Bismarck, North Dakota
Learn Security in Bismarck, NorthDakota and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current Security related training offerings in Bismarck, North Dakota: Security Training
Security Training Catalog
AWS Classes
JUnit, TDD, CPTC, Web Penetration Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
C# PROGRAMMING –MAIN DESIGN GOALS
C# is a popular programming language these days, and it was designed from inception to provide a simple, clean, general purpose programming language for those intending to work within the confines of Microsoft’s .NET framework. Since then, it has been approved as one of the standard languages by both ECMA and ISO, making C# programming an essential tool in every programmers’ kit.
Different languages have different uses and specialties, and C# was designed for programmers to be able to use it to create different components for use in software that would be deployed and distributed en masse, to live use environments. This means that designers had to really put an emphasis on making the actual source code extremely compatible and portable. Those already familiar with C or C++ should definitely notice this emphasis.
Another particular point of emphasis during design was focus on internationalization of the language; it was intended from inception to be available all over the world, and to see all sorts of different implementations based on variance in regional programming technique. The resultant use should help the language develop sophistication as it is refined throughout different versions.
The original article was posted by Michael Veksler on Quora
A very well known fact is that code is written once, but it is read many times. This means that a good developer, in any language, writes understandable code. Writing understandable code is not always easy, and takes practice. The difficult part, is that you read what you have just written and it makes perfect sense to you, but a year later you curse the idiot who wrote that code, without realizing it was you.
The best way to learn how to write readable code, is to collaborate with others. Other people will spot badly written code, faster than the author. There are plenty of open source projects, which you can start working on and learn from more experienced programmers.
Readability is a tricky thing, and involves several aspects:
- Never surprise the reader of your code, even if it will be you a year from now. For example, don’t call a function max() when sometimes it returns the minimum().
- Be consistent, and use the same conventions throughout your code. Not only the same naming conventions, and the same indentation, but also the same semantics. If, for example, most of your functions return a negative value for failure and a positive for success, then avoid writing functions that return false on failure.
- Write short functions, so that they fit your screen. I hate strict rules, since there are always exceptions, but from my experience you can almost always write functions short enough to fit your screen. Throughout my carrier I had only a few cases when writing short function was either impossible, or resulted in much worse code.
- Use descriptive names, unless this is one of those standard names, such as i or it in a loop. Don’t make the name too long, on one hand, but don’t make it cryptic on the other.
- Define function names by what they do, not by what they are used for or how they are implemented. If you name functions by what they do, then code will be much more readable, and much more reusable.
- Avoid global state as much as you can. Global variables, and sometimes attributes in an object, are difficult to reason about. It is difficult to understand why such global state changes, when it does, and requires a lot of debugging.
- As Donald Knuth wrote in one of his papers: “Early optimization is the root of all evil”. Meaning, write for readability first, optimize later.
- The opposite of the previous rule: if you have an alternative which has similar readability, but lower complexity, use it. Also, if you have a polynomial alternative to your exponential algorithm (when N > 10), you should use that.
Use standard library whenever it makes your code shorter; don’t implement everything yourself. External libraries are more problematic, and are both good and bad. With external libraries, such as boost, you can save a lot of work. You should really learn boost, with the added benefit that the c++ standard gets more and more form boost. The negative with boost is that it changes over time, and code that works today may break tomorrow. Also, if you try to combine a third-party library, which uses a specific version of boost, it may break with your current version of boost. This does not happen often, but it may.
Don’t blindly use C++ standard library without understanding what it does - learn it. You look at std::vector::push_back()std::mapstd::unordered_map
Never call newdeletestd::make_uniqueusique_ptr, shared_ptr, weak_ptr
Every time you look at a new class or function, in boost or in std, ask yourself “why is it done this way and not another?”. It will help you understand trade-offs in software development, and will help you use the right tool for your job. Don’t be afraid to peek into the source of boost and the std, and try to understand how it works. It will not be easy, at first, but you will learn a lot.
Know what complexity is, and how to calculate it. Avoid exponential and cubic complexity, unless you know your N is very low, and will always stay low.
Learn data-structures and algorithms, and know them. Many people think that it is simply a wasted time, since all data-structures are implemented in standard libraries, but this is not as simple as that. By understanding data-structures, you’d find it easier to pick the right library. Also, believe it or now, after 25 years since I learned data-structures, I still use this knowledge. Half a year ago I had to implemented a hash table, since I needed fast serialization capability which the available libraries did not provide. Now I am writing some sort of interval-btree, since using std::map, for the same purpose, turned up to be very very slow, and the performance bottleneck of my code.
Notice that you can’t just find interval-btree on Wikipedia, or stack-overflow. The closest thing you can find is Interval tree, but it has some performance drawbacks. So how can you implement an interval-btree, unless you know what a btree is and what an interval-tree is? I strongly suggest, again, that you learn and remember data-structures.
These are the most important things, which will make you a better programmer. The other things will follow.
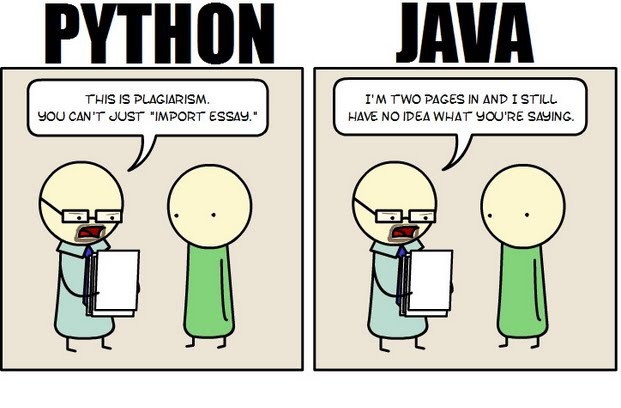 Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
Java still has its place in the world of software development, but is it quickly becoming obsolete by the more dynamically enabled Python programming language? The issue is hotly contested by both sides of the debate. Java experts point out that Java is still being developed with more programmer friendly updates. Python users swear that Java can take up to ten times longer to develop. Managers that need to make the best decision for a company need concrete information so that an informed and rational decision can be made.
First, Java is a static typed language while Python is dynamically typed. Static typed languages require that each variable name must be tied to both a type and an object. Dynamically typed languages only require that a variable name only gets bound to an object. Immediately, this puts Python ahead of the game in terms of productivity since a static typed language requires several elements and can make errors in coding more likely.
Python uses a concise language while Java uses verbose language. Concise language, as the name suggests, gets straight to the point without extra words. Removing additional syntax can greatly reduce the amount of time required to program. A simple call in Java, such as the ever notorious "Hello, World" requires three several lines of coding while Python requires a single sentence. Java requires the use of checked exceptions. If the exceptions are not caught or thrown out then the code fails to compile. In terms of language, Python certainly has surpassed Java in terms of brevity.
Additionally, while Java's string handling capabilities have improved they haven't yet matched the sophistication of Python's. Web applications rely upon fast load times and extraneous code can increase user wait time. Python optimizes code in ways that Java doesn't, and this can make Python a more efficient language. However, Java does run faster than Python and this can be a significant advantage for programmers using Java. When you factor in the need for a compiler for Java applications the speed factor cancels itself out leaving Python and Java at an impasse.
While a programmer will continue to argue for the language that makes it easiest based on the programmer's current level of knowledge, new software compiled with Python takes less time and provides a simplified coding language that reduces the chance for errors. When things go right, Java works well and there are no problems. However, when errors get introduced into the code, it can become extremely time consuming to locate and correct those errors. Python generally uses less code to begin with and makes it easier and more efficient to work with.
Ultimately, both languages have their own strengths and weaknesses. For creating simple applications, Python provides a simpler and more effective application. Larger applications can benefit from Java and the verbosity of the code actually makes it more compatible with future versions. Python code has been known to break with new releases. Ultimately, Python works best as a type of connecting language to conduct quick and dirty work that would be too intensive when using Java alone. In this sense, Java is a low-level implementation language. While both languages are continuing to develop, it's unlikely that one language will surpass the other for all programming needs in the near future.

Jeff Nelson, a former Googler and inventor of Chromebook says on Quora, “One habit I've clung to is writing small prototypes when I'm trying to learn new concepts.
For example, I'll sit down with a book or a web page, and over the course of a few hours, write 30 or 40 programs all of them only a few dozen lines long. Each program intended to demonstrate some simple concept. This prototyping makes it very easy to try out many concepts in a short period of time.”
Miguel Paraz, Software Engineering Student habit is to “keep a log in a text file or document on my work computer. Before trying to solve a problem, I write it down first. And then I describe the details as they happen.”
Tech Life in North Dakota
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in North Dakota since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about Security programming
- Get your questions answered by easy to follow, organized Security experts
- Get up to speed with vital Security programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
