JUnit, TDD, CPTC, Web Penetration Training Classes in Concord, New Hampshire
Learn JUnit, TDD, CPTC, Web Penetration in Concord, NewHampshire and surrounding areas via our hands-on, expert led courses. All of our classes either are offered on an onsite, online or public instructor led basis. Here is a list of our current JUnit, TDD, CPTC, Web Penetration related training offerings in Concord, New Hampshire: JUnit, TDD, CPTC, Web Penetration Training
JUnit, TDD, CPTC, Web Penetration Training Catalog
subcategories
Android and iPhone Programming Classes
Course Directory [training on all levels]
- .NET Classes
- Agile/Scrum Classes
- AI Classes
- Ajax Classes
- Android and iPhone Programming Classes
- Azure Classes
- Blaze Advisor Classes
- C Programming Classes
- C# Programming Classes
- C++ Programming Classes
- Cisco Classes
- Cloud Classes
- CompTIA Classes
- Crystal Reports Classes
- Data Classes
- Design Patterns Classes
- DevOps Classes
- Foundations of Web Design & Web Authoring Classes
- Git, Jira, Wicket, Gradle, Tableau Classes
- IBM Classes
- Java Programming Classes
- JBoss Administration Classes
- JUnit, TDD, CPTC, Web Penetration Classes
- Linux Unix Classes
- Machine Learning Classes
- Microsoft Classes
- Microsoft Development Classes
- Microsoft SQL Server Classes
- Microsoft Team Foundation Server Classes
- Microsoft Windows Server Classes
- Oracle, MySQL, Cassandra, Hadoop Database Classes
- Perl Programming Classes
- Python Programming Classes
- Ruby Programming Classes
- SAS Classes
- Security Classes
- SharePoint Classes
- SOA Classes
- Tcl, Awk, Bash, Shell Classes
- UML Classes
- VMWare Classes
- Web Development Classes
- Web Services Classes
- Weblogic Administration Classes
- XML Classes
- ASP.NET Core MVC, Rev. 8.0
15 June, 2026 - 16 June, 2026 - AWS Certified Machine Learning: Specialty (MLS-C01)
20 July, 2026 - 24 July, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN I
22 June, 2026 - 26 June, 2026 - RED HAT ENTERPRISE LINUX SYSTEMS ADMIN II
29 June, 2026 - 2 July, 2026 - See our complete public course listing
Blog Entries publications that: entertain, make you think, offer insight
Like me, I believe most people go about their business never to give a serious thought about their assumed private correspondence when using Gmail to email friends, colleagues and business associates. As it turns out, your daily banter may not be so private after all. A recent article in Fortune Magazine, “Judge Rejects Google Deal Over Email Scanning” caught my attention and an immediate thought dominated my curiosity…Google email and scanning scam.
In essence, the article describes Googles’ agreement to change the way it scans incoming messages so that it no longer reads emails while they are in transit, but only when they are in someone's inbox! So, what exactly does that mean? Judge Koh, a San Francisco federal judge, said she's not so sure about that. Her ruling claims the settlement does not provide an adequate technical explanation of Google's workaround, which involves scanning in-transit emails for security purposes, and then later parsing them for advertising data. The judge also proposed a legal settlement to pay $2.2 million to lawyers, but nothing to consumers.
My interest in this story is not so much about the proposed settlements or the specific details about how Google or any of the web giants settle claims based on vague legal language. It is however, more about the naiveté of myself and perhaps many others that never question how the email scanning process really works. I wonder, do most of us really care that Gmail uses contents of our mail to display targeted ads?
Information Technology is one of the most dynamic industries with new technologies surfacing frequently. In such a scenario, it can get intimidating for information technology professionals at all levels to keep abreast of the latest technology innovations worth investing time and resources into.
It can therefore get daunting for entry and mid-level IT professionals to decide which technologies they should potentially be developing skills. However, the biggest challenge comes for senior information technology professionals responsible for driving the IT strategy in their organizations.
It is therefore important to keep abreast of the latest technology trends and get them from reputable sources. Here are some of the ways to keep on top of the latest trends in Information Technology.
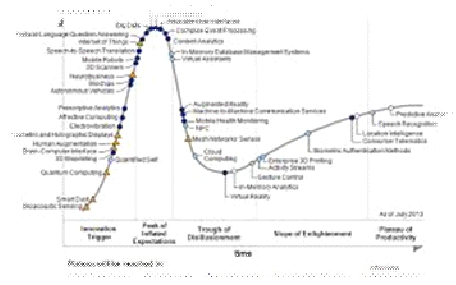
· Subscribe to leading Analyst Firms: If you work for a leading IT organization, chances are that you already have subscription to leading IT analyst firms notably Gartner and Forrester. These two firms are some of the most recognized analyst firms with extensive coverage on almost every enterprise technology including hardware and software. These Analyst firms frequently publish reports on global IT spending and trends that are based on primary research conducted on vendors and global CIOs & CTOs. However, subscription to these reports is very expensive and if you are a part of a small organization you may have issues securing access to these reports. One of the most important pieces of research published by these firms happens to be the Gartner Hype Cycle which plots leading technologies and their maturity curve.Even if you do not have access to Gartner research, you can hack your way by searching for “Gartner Hype Cycle” on Google Images and you will in most cases be able to see the plots similar to the one below
 Straight up and full disclosure. I'm prejudiced. As a research assignment, the heading is a joke. I'll give you the answer in two words, and then tell you why.
Straight up and full disclosure. I'm prejudiced. As a research assignment, the heading is a joke. I'll give you the answer in two words, and then tell you why.
How does HTML 5 compare with flash? Answer: it doesn't.
Lest you think I dislike Adobe's Flash, let's put the cards on the table. I loved Flash. Long before Adobe was Adobe, they had a competitor called Macromedia. Adobe bought that firm. That made my life simpler. I only had to work with one vendor.
Flash was a pretty compelling solution. I used it to mimic operations in Windows to prepare people for the CompTIA exams. The only bugaboo was that dang right-click stuff. A little bit of code from the Microsoft Visual Studio .Net let me flip the left and right mouse buttons so that the right mouse button instead of controlling the Flash player, emulated doing a right-click in the Windows operating system.
Once again theTIOBE Programming Community has calculated the trends in popular programming languages on the web. Evaluating the updates in the index allows developers to assess the direction of certain programming skills that are rising or faltering in their field. According to the November 2013 report, three out of four languages currently ranking in the top twenty are languages defined by Microsoft. These are C#, SQL Server language Transact-SQL and Visual Basic.NET. Not surprising though, the top two languages that remain steady in the number one and two spots are Java and C.
How are the calculations measured? The information is gathered from five major search engines: Google, Bing, Yahoo!, Wikipedia, Amazon, YouTube and Baidu.
Top 20 Programming Languages: as of November 2013
- C
- Java
- Objective-C
- C++
- C#
- PHP
- (Visual) Basic
- Python
- Transact-SQL
- Java Script
- Visual Basic.NET
- Perl
- Ruby
- Pascal
- Lisp
- MATLAB
- Delphi/Object Pascal
- PL/SQL
- COBOL
- Assembly
Although the index is an important itemized guide of what people are searching for on the internet, it’s arguable that certain languages getting recognition is a direct result of early adopters posting tutorials and filling up discussion boards on current trends. Additionally, popular tech blogs pick up on technological shifts and broadcast related versions of the same themes.
When does the popularity of a software language matter?
- If you want marketable skills, knowing what employers are looking for is beneficial. As an example, languages such as Java and Objective C are highly coveted in the smart-phone apps businesses.
- A consistently shrinking language in usage is an indicator not only that employers are apt to pass on those skills but fall in danger of being obsolete.
- Focusing on languages that are compatible with other developers increases your chances to participate on projects that companies are working on.
Tech Life in New Hampshire
training details locations, tags and why hsg
The Hartmann Software Group understands these issues and addresses them and others during any training engagement. Although no IT educational institution can guarantee career or application development success, HSG can get you closer to your goals at a far faster rate than self paced learning and, arguably, than the competition. Here are the reasons why we are so successful at teaching:
- Learn from the experts.
- We have provided software development and other IT related training to many major corporations in New Hampshire since 2002.
- Our educators have years of consulting and training experience; moreover, we require each trainer to have cross-discipline expertise i.e. be Java and .NET experts so that you get a broad understanding of how industry wide experts work and think.
- Discover tips and tricks about JUnit, TDD, CPTC, Web Penetration programming
- Get your questions answered by easy to follow, organized JUnit, TDD, CPTC, Web Penetration experts
- Get up to speed with vital JUnit, TDD, CPTC, Web Penetration programming tools
- Save on travel expenses by learning right from your desk or home office. Enroll in an online instructor led class. Nearly all of our classes are offered in this way.
- Prepare to hit the ground running for a new job or a new position
- See the big picture and have the instructor fill in the gaps
- We teach with sophisticated learning tools and provide excellent supporting course material
- Books and course material are provided in advance
- Get a book of your choice from the HSG Store as a gift from us when you register for a class
- Gain a lot of practical skills in a short amount of time
- We teach what we know…software
- We care…
